A penetration test, colloquially known as a pen test, is an authorized simulated cyber attack on a computer system, performed to evaluate the security of the system.[promotional or fringe source?] The test is performed to identify both weaknesses (also referred to as vulnerabilities), including the potential for unauthorized parties to gain access to the system's features and data, as well as strengths, enabling a full risk assessment to be completed.
The process typically identifies the target systems and a particular goal, then reviews available information and undertakes various means to attain that goal. A penetration test target may be a white box (which provides background and system information) or black box (which provides only basic or no information except the company name). A gray box penetration test is a combination of the two (where limited knowledge of the target is shared with the auditor).[promotional or fringe source?] A penetration test can help determine whether a system is vulnerable to attack if the defenses were sufficient, and which defenses (if any) the test defeated.
Security issues that the penetration test uncovers should be reported to the system owner. Penetration test reports may also assess potential impacts to the organization and suggest countermeasures to reduce risk.
The National Cyber Security Center, describes penetration testing as the following: "A method for gaining assurance in the security of an IT system by attempting to breach some or all of that system's security, using the same tools and techniques as an adversary might."
The goals of a penetration test vary depending on the type of approved activity for any given engagement with the primary goal focused on finding vulnerabilities that could be exploited by a nefarious actor and informing the client of those vulnerabilities along with recommended mitigation strategies.
Penetration tests are a component of a full security audit. For example, the Payment Card Industry Data Security Standard requires penetration testing on a regular schedule, and after system changes.
https://en.wikipedia.org/wiki/Penetration_test
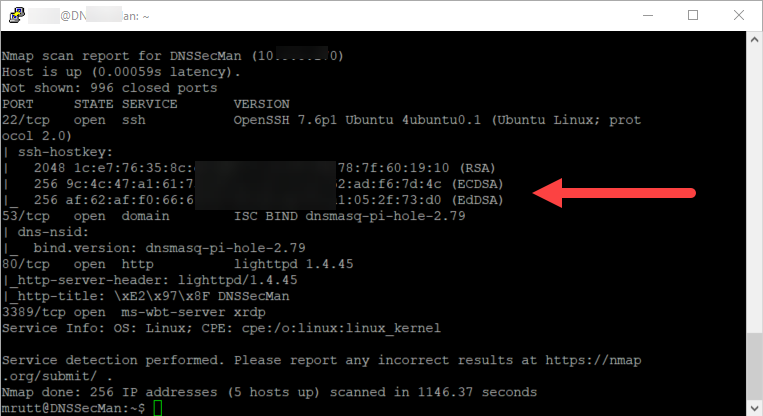
Below you will see a phase two scan using NMAP. NMAP is the go to scanning tool for penetration testers. It will give you a lot of good information depending on the type of scan you run. Here you see what ports are open to attack.
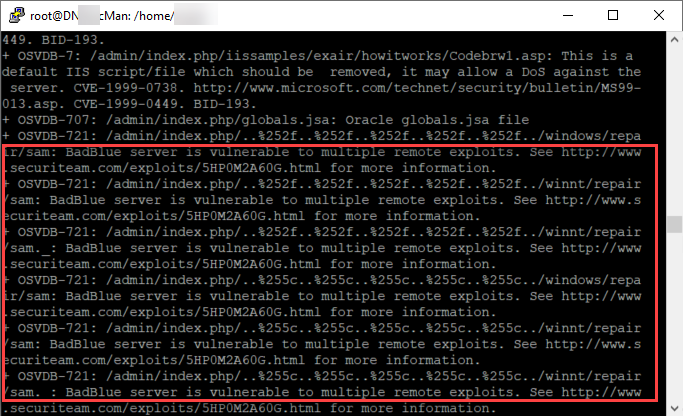
Since this was a web server my go to tool was Nikto. Nikto will tell you what web vulnerabilities exist and are open to exploit or in my case what needs needs to be patched.
It's always important to know what your attack surface looks like an what needs to have security controls in place. Knowing the assets you have and what data resides on those hosts will tell you how many resources will have to be dedicated to protect the asset.